Many years later, social engineering is still one of the most powerful tools in the arsenal when it comes to gaining access to sensitive data and critical systems within an organization. The premise behind social engineering is to exploit the human factor. In other words, putting people in situations to where they have to make a conscious decision to either interact with or ignore a potential threat.
Common human nature weaknesses:
- The desire to be helpful
- The tendency to trust other people
- The fear of getting in trouble
- Conflict avoidance
Vonahi Security Social Engineering Tactics:
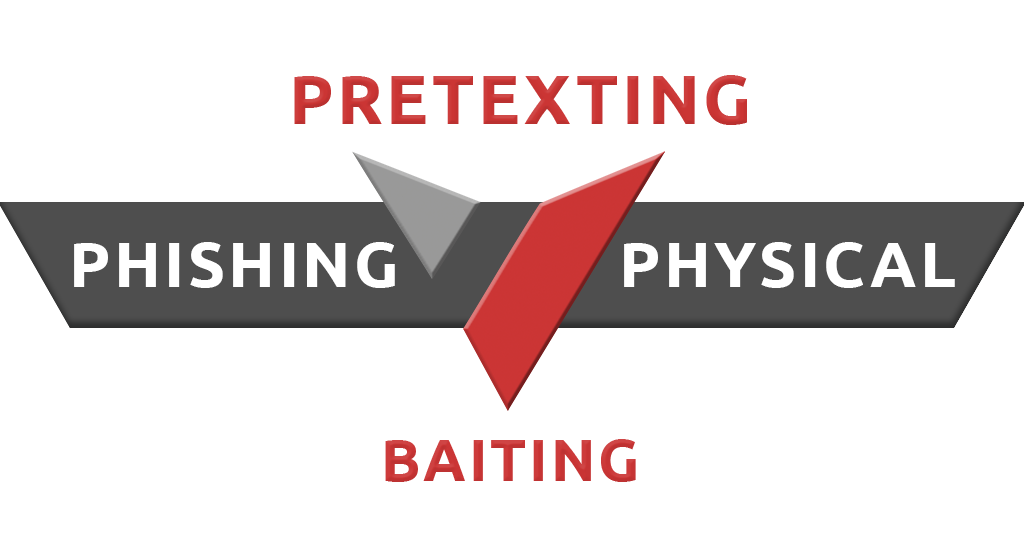
Pretexting
- The art of placing a person in a realistic, but fake, situation to extract information from the individual
- Example: Impersonating a help desk employee to trick the employee into downloading an update/malware on their system
Phishing
- Sending fraudulent emails in order to coerce people into executing malicious actions or revealing importation information. These emails are usually crafted to appear like a legitimate company email
- Whaling: Targets executives in an organization
- Spear Phishing: Highly targeted to specific individual within the organization
Physical
- Gaining physical access to a facility or restructured area
- Impersonation is the key for gaining physical access. An individual will utilize impersonation to accomplish this goal by acting as another individual to gain access
- Example: Impersonating pest control or network technicians in order to access secure areas within the facility
- Tailgating/Piggybacking refers to when a person tags along with another person who is authorized to gain entry into a restricted area, or pass a certain checkpoint
- Impersonation is the key for gaining physical access. An individual will utilize impersonation to accomplish this goal by acting as another individual to gain access
Baiting
- Baiting is also defined as the human curiosity factor and is a basic trait in human nature
- Example: USB Drops entices the curiosity factor of an individual to inspect the elements on the USB. Once opened, access to their systems may be granted to the attacker, or data is exfiltrated
How can we help?
In today’s world, conducting social engineering assessments once a year is not enough to effectively make an impact within your environment. It is common for employees to simply interact with a phishing attack, take a training course, and continue performing these bad habits. In addition to periodic training, testing your employees against social engineering attacks should occur multiple times a year, depending on the scope of engagement, costs, etc.
At Vonahi Security, we offer social engineering assessments that focus on weaknesses in physical and human factor social domains. We conduct these assessments on a regular basis to help our clients evaluate their security controls and help them understand business impact through:
Social Engineering (SE) Assessments:
- Review of social engineering security risk evaluation based on full scope threat modeling
- Assessment of employees’ susceptibility to social engineering attacks through various social engineering attack scenarios
Physical Security Assessments:
- Review of physical security risk evaluation based on full scope threat modeling
- Identify physical security weaknesses through on-site adversary simulations
We’ve conducted hundreds of social engineering assessments and can provide strategic recommendations to helping your organization improve its human and physical security posture.
About Vonahi Security
Vonahi Security is a cybersecurity consulting firm that offers modern consulting services to help organizations achieve both compliance and security best practices. With over 30 years of combined industry experience in both offensive and defensive security operations, our team of certified consultants have experience working with a significant number of organizations, industries, networks, and technologies. Our service expertise includes Managed Security, Adversary Simulations, Strategy & Review, and User Education & Awareness. Vonahi Security is headquartered in Atlanta, GA. To learn more, visit www.vonahi.io
Stay Informed
