Interacting with PDF documents is a normal part of day-to-day business operations for many organizations. In many cases, this is the preferred file format to electronically transfer important and sensitive information, such as policies, procedures, bank statements, electronic W2 forms, customer-related information, and more.
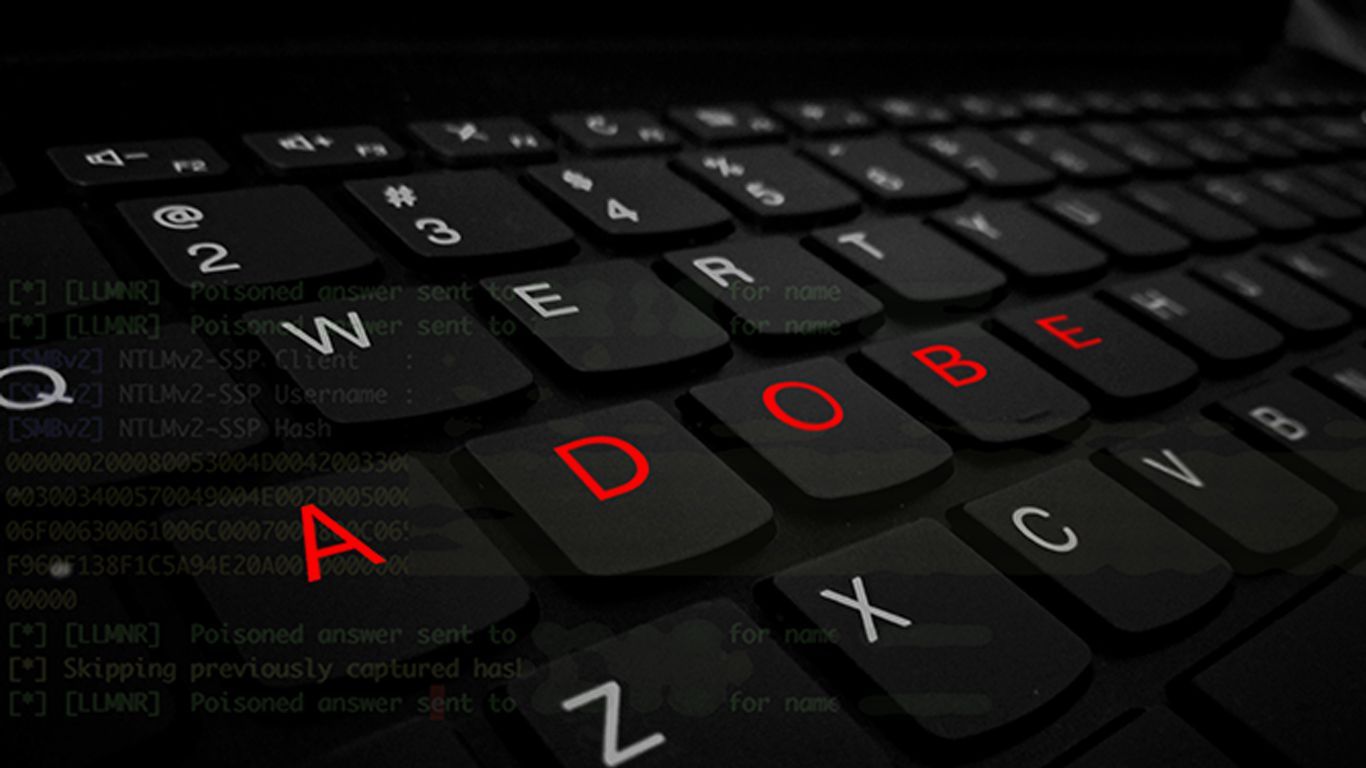
In a recent post published by a security researcher over at Check Point, it was discovered that a feature within PDF documents, specifically when using Adobe Reader or Foxit PDF reader, could be leveraged to obtain hashed user credentials from a user simply opening a PDF document [1]. After the researcher disclosed the newly discovered attack vector to Adobe, the company stated that Microsoft had already provided customers the ability to disable the way user accounts authenticate. Additionally, Adobe indicated in their statement to Check Point that there were no plans on making any changes in the PDF reader software to prevent such an attack from occurring.
How This Could Affect Your Organization
Although it is possible for an attacker to obtain hashed credentials from the user, whether or not they are able to actually use the credentials to perform malicious attacks depends on the complexity of the user's password. If an attacker is successful with recovering the clear-text value of the user's account credentials, it may be possible to perform a number of actions, including some of the following:
- Access to the compromised user's email inbox
- Unauthorized access to system resources, depending on the permission levels of the user
- Impersonation or spoof of the user account, leading to additional compromises
Having access to a user's user account credentials could pose a significant threat to the confidentiality and integrity of sensitive documents that the user may have access to.
Mitigation Strategies to Help Protect Your End-Users
Protecting your end-users against these types of security threats can be a challenging process, especially considering the many different avenues that attackers can take. In the case of this specific discovery, attackers would most likely attempt to compromise user account credentials through the form of social engineering attacks. To aid with ensuring your end-users are protected and well-prepared for such attacks, the following recommendations should be taken into consideration.
Password Complexity
Having a strong, complex password could essentially increase the difficulty for an attacker to recover the clear-text version of hashed credentials. Your organization should ensure that password policies meet security best practices and industry standards for securing credentials.
Although having a complex password would reduce the chances of an attacker being successful with this attack, the chances of successfully guessing or recovering your account credentials through other methods are much lower.
User Awareness Training
Ensuring your organization has a mature user awareness training program can be one of the most significant ways to ensure your critical data and systems are protected from attackers. While investing in modern and advanced technology can serve as protection, properly trained end-users can be extremely effective to reducing your overall attack surface.
In addition to ensuring a mature user awareness training program exists within your organization, assessments to determine your end-users' susceptibility to social engineering attack should be performed. Using the results of these assessments, your user awareness training program can be fine-tuned to improve areas where end-users are falling short.
Modifying Microsoft's Authentication Procedures
As mentioned in Adobe's response to Check Point, Microsoft released an optional security enhancement that provides customers with the ability to disable NT LAN Manager (NTLM) single sign-on (SSO) authentication, which would prevent such an attack from occurring within a PDF [2]. It should be noted, however, that disabling NTLM SSO authentication could potentially affect other services within the organization and, as a precaution, testing is highly recommended.
References:
[1] https://research.checkpoint.com/ntlm-credentials-theft-via-pdf-files
[2] https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/ADV170014
About Vonahi Security
Vonahi Security is a cybersecurity consulting firm that offers modern consulting services to help organizations achieve both compliance and security best practices. With over 30 years of combined industry experience in both offensive and defensive security operations, our team of certified consultants have experience working with a significant number of organizations, industries, networks, and technologies. Our service expertise includes Managed Security, Adversary Simulations, Strategy & Review, and User Education & Awareness. Vonahi Security is headquartered in Atlanta, GA.
Stay Informed